Social Phishing
The term ‘phishing’ was first coined by the famous hacker and spammer Khan C. Smith in 1990s. Wikipedia defines phishing as the fraudulent attempt to obtain sensitive information, by disguising as a trustworthy entity in an electronic communication. However, phishing might also occur through online social media, otherwise known as Social Phishing.
Phishing attacks via emails, prompting users to click malicious links or divulge personal information such as credit card number or password are well known. We have heard of numerous stories of emails with Nigerian princes asking for financial favours or your bank supposedly asking you to reset your password urgently. However, what most of us forget is social media as a great vector of attack in today’s age. In Social Media, people generally view content posted by their friends, family and companies or brands they chose to follow. This creates a trusted environment, different from that of emails, inundated with spam. This feeling of security along with the widespread use of social media networks attracts phishers.
Aim and Motivation
AIM:
The aim of our project was to
- Find the level of susceptibility of students at IIIT-H to social phishing
- Analyze the process involved
- Recognize which demographic is more susceptible and
- Raise awareness among the students regarding such attacks
MOTIVATION:
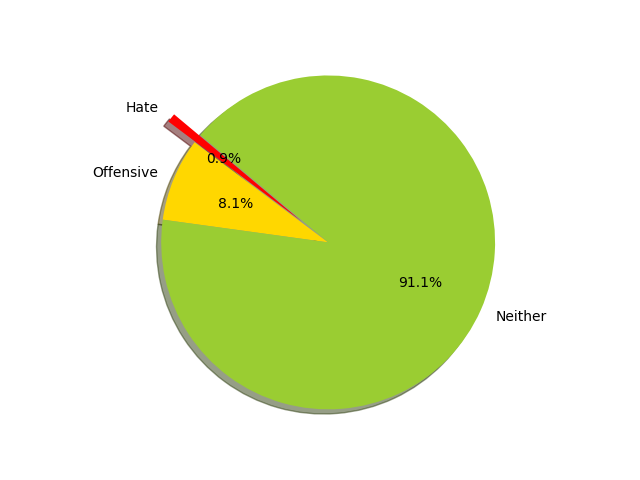
Given that there are a large number of subscribers on different social media platforms, phishing attacks on online social networks is on the rise. Here are some statistics from 2016:
Method
To test IIIT-H’s awareness of social phishing, we first sent out a questionnaire, asking them for their opinion on privacy and security in online social media. We then used their responses to formulate our vector of attack. Based on their responses, we chose three social media networks to infiltrate, sent out requests within the community and then analyzed the results.
Our survey
We first asked people which social media services they used. Based on their responses, we chose Instagram, Facebook and LinkedIn which seemed to be among the most popular.
We then asked people about their experience with phishing on social media. It seemed like 2/3rds of them had never been phished. About 15% of them had been phished via emails.
Consequently, we asked people about the steps they take to ensure privacy and security online.
Finally, we allowed people to evaluate how susceptible they thought they were to phishing and how privacy-conscious they were.
We then moved on to create a fake account on each of the social media websites, send out connection requests and analyze the response.
In Facebook, we created the profile of a girl named Neha Aggarwal from IIIT - Delhi. Out of the 210 requests sent out, 73 people accepted the friend request.
We plotted the cumulative graph between the number of hours passed since the friend requests were sent and the number of people who accepted it. We found that approximately six hours after the messages were sent was the peak acceptance time for those friend requests.
We also drew a graph showing the relative percentages of the students in each batch who accepted the friend requests. We found that first years and interns and PGSSP students (classified as other in the graph) were most vulnerable to accepting requests from our fake account.
We created a fake profile on LinkedIn as well and provided this account with a more fleshed out backstory with information about his workplace, an obscure university in Europe and prior connections. We changed the privacy settings to try to hide the fact that the account was fake. We sent out connection requests to people requesting information for summer internships.
We sent around 200 connection requests to IIIT students on LinkedIn. Around 70% of the people who accepted the invitations also filled the form for further details that we requested.
Approximately 90% of the people who filled the forms provided resume details. Resumes contain addresses and phone numbers and other personal sensitive information and thus this was a scarily effective phishing attack.
We found that a majority of the people who accepted friend requests on facebook were boys. So we decided to do a gender analysis on Instagram.
We created two fake accounts, one male and one female. Each one was attached to a stock image profile and a stock image post with generic profile description. We sent 260 follow requests from each account to students in IIIT.
As expected the female account received more accepts and follow back requests as compared to the male one. The above graph shows the incoming and outgoing connections for the male and female accounts.
Another interesting observation is the fact that most of the people who accepted the male account’s request had also accepted the female account’s request. This seems to lead to the conclusion that there is a nucleus of people who accept all requests sent to them and those are the people that accepted the boy’s requests.
Results and conclusions
We compared people's tendency to accept requests on Facebook, Instagram and LinkedIn. In the graph below each vertical line represents one subject, where the blue dot represents Facebook, the red Instagram and the yellow LinkedIn. If the subject was phished on all three sites, he will have a dot in every row.
We also analyzed the responses of people who got phished, regarding their opinion of their susceptibility. Most people who got phished had initially responded to the survey very confidently about their privacy consciousness. They rated themselves 4/5 in privacy consciousness and mostly thought their susceptibility to phishing scams is about 2/5. This shows that often people, who have lesser exposure, tend to be ignorant of the possible risk and fall prey to such scams.
Some tips to stay safe on social media:
- Don’t click unidentified links. Think before you click! Google’s Transparency report on Safe Browsing is a useful website to check links before clicking on them.
- Don’t accept requests from strangers or send sensitive information to them.
- If you suspect an account is fake, reverse search the profile picture to ensure authenticity.
Comments
Post a Comment